Building a Suite of Scalable, Defensible Cybersecurity Policy Templates
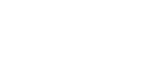
Developing a consistent, scalable, and defensible cybersecurity program begins with a solid cybersecurity policy framework. A well-designed policy framework ensures clear responsibility, audit defensibility, and efficient customization across different environments.
This article will guide you through building a suite of cybersecurity policy templates that teams can tailor to each client while maintaining consistency and scalability. Each section will begin by covering the structure of an individual policy, why each component exists, and how elements are cross-referenced between policies.
Summary of cybersecurity policy template components
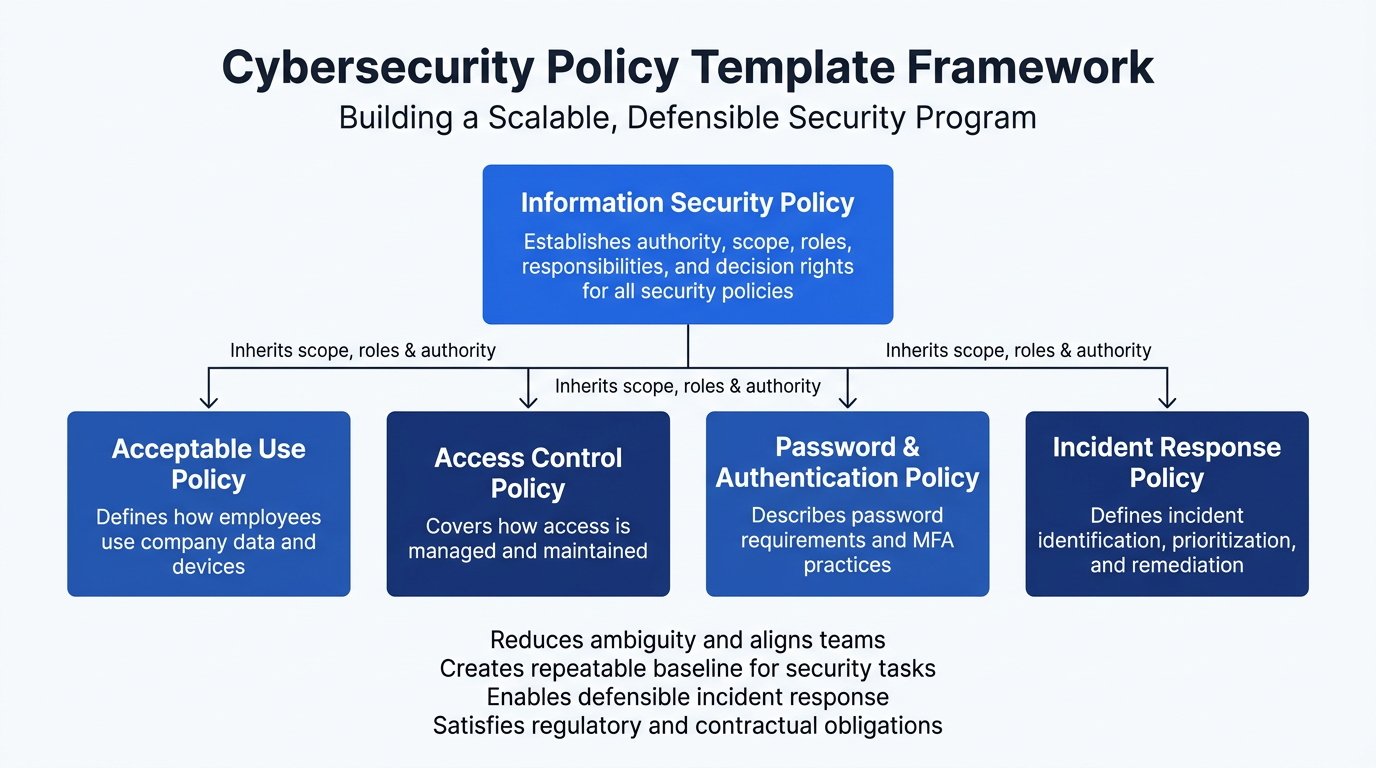
Important: The policy components listed below represent a baseline for a standard cybersecurity program; however, this list is not exhaustive. Depending on your organization’s unique risk profile and the specific compliance or regulatory frameworks you operate under (such as HIPAA, GDPR, or SOC 2), additional policies may be required.
Furthermore, these descriptions are not prescriptive. These templates must be modified and tailored to align with your specific operational requirements, legal obligations, and internal governance structures.
The purpose of cybersecurity policies
Policies are not just a box to be checked to get cybersecurity insurance; they are the source of authority for security decisions that turn objectives into day-to-day action. From an operational perspective, clear policies reduce ambiguity, align teams on responsibilities and expectations, and create a repeatable baseline for most information-technology-related tasks and security items. A formal set of policies should define scope, roles, responsibilities, and approval paths, allowing daily tasks to be efficient, change control to be a value-add, and exceptions to be properly documented.
Well-written policies should do the following:
- Define purpose and scope
- Assign roles, responsibilities, and decision rights
- Establish approval paths and exception handling
- Map controls to recognized frameworks
- Specify measurable requirements and evidence of compliance
- Balance prescriptive standards with risk-based flexibility
- Align operations across teams and vendors
- Document due diligence and due care
- Satisfy legal, regulatory, and contractual obligations
- Enable defensible incident response and audit readiness
- Include clear ownership, versioning, and a scheduled review cadence
{{banner-large-1="/inline-cards"}}
Information security policy
The information security (IS) policy is the root of all other policies. It establishes authority, outlines how the organization protects information technology assets, explains why that protection is essential, and identifies who is empowered to make and enforce security decisions. This policy exists to translate strategy into actionable items, enabling teams to operate under a single set of expectations.
Objective and intent
This section should define the organization's information security values and explain why. For instance, if the organization is subject to regulation or is positioned to gain a competitive advantage from uptime, privacy, or confidentiality of intellectual property, that information should be provided.
This section anchors the classic objectives of confidentiality, integrity, and availability as described by NIST. It establishes the organization’s commitment to implementing reasonable, risk-based safeguards and to pursuing continuous improvement under executive ownership.
Why this matters
This section defines the scope of the Information Security Policy, including the people, processes, systems, data, facilities, environments, and third parties that store, process, or transmit organizational information, and documents any exclusions with an assigned owner and review date, while also explaining why protecting these assets is essential to the organization’s success. Information security supports regulatory compliance, operational resilience, customer trust, contractual obligations, and protection of intellectual property by safeguarding confidentiality, integrity, and availability; by clearly linking defined scope to business purpose in a single statement, the policy establishes governance boundaries, reinforces accountability, and strengthens the consistency and defensibility of the entire policy suite.
Operational and legal rationale
This section should articulate why information security matters to the client in question. These statements provide justification for actions in subsequent documents. The rationale should be stated in terms of business objectives such as regulatory obligations, operational uptime, customer trust, or protection of intellectual property, and should be anchored to the classic security objectives of confidentiality, integrity, and availability. The section should also include a clear statement of leadership’s commitment to risk-based safeguards and continuous improvement. This is not a technical section; it is a business intent statement that will inform all other policies.
Scope, roles, responsibilities, and authority
This is the most important structural section in the entire suite. The template must require the organization to define:
- What systems, data, users, and environments are in scope (and what are not)
- Who is responsible for governance functions such as incident response, risk management, and policy maintenance
- Who has the authority to enforce policy, approve exceptions, and accept risk
This section should be written with service providers’ delivery models in mind. It must clearly distinguish between client responsibilities and provider responsibilities, and define escalation paths and decision rights. Every other policy should reference this section instead of redefining ownership or authority locally.
A useful test when templating this section is simple: If another policy needs to say “who decides” or “who is responsible,” that information should already exist here.
Framework and policy hierarchy
The template should explicitly state that this policy provides the framework for all other security policies and standards. It should call out that the scope, roles, responsibilities, authority, and exception handling defined here are inherited by downstream policies unless a specific policy states otherwise.
Compliance and defensibility
The template should position this policy as the organization’s primary evidence of due diligence and due care. For many frameworks and governing bodies, this is the first document reviewed to assess security governance maturity. It is often the starting point for alignment to frameworks, a requirement for cyber insurance, and a cornerstone of audit defensibility. The policy should explicitly state that it establishes a baseline against which compliance, risk acceptance, and enforcement are measured.
Acceptable use policy
This policy sets expectations for how workforce members use organizational systems, data, and services. It exists to reduce human error and risky behavior that could negatively impact the organization's overall security posture and objectives.
Scope
The AUP should inherit its scope, roles, and authority model from the information security policy. Do not redefine who has decision rights, who approves exceptions, or who enforces discipline here. This policy should explicitly reference those provisions in the information security policy and rely on them. The AUP is about behavioral rules, not governance structure or roles.
Authorized and prohibited use
This section should be organized around categories that can be tuned per client:
- Company devices, networks, and services: Define what business use means and if limited personal use is acceptable or not.
- Organizational data: Set expectations on where data can and cannot be stored. Do not use phrases like “secure storage” that are subjective; define the exact terms you wish to use.
- Software and services: Address unauthorized software and shadow IT with language that can be tightened or loosened based on the client.
- Work models: State whether the rules change or remain the same for BYOD scenarios.
Avoid absolute statements that will cause friction in real-world operations; instead, define principles and then list examples.
Ownership, monitoring and legal standing
The template must establish that devices, accounts and data are corporate assets, so use of them may be monitored and logged. The template should also state that users should have no expectation of privacy when using company systems. This is a legal protection that should be in place for all clients.
Risk
When creating your template, tie the rules to concrete risks the policy is meant to reduce. Use the objectives defined in the information security policy to guide which risks to consider, which helps justify controls and disputes, making the policy more defensible.
Enforcement and consequences
This section should not create a new disciplinary framework. The AUP should clearly state that systems are monitored, that suspected violations may trigger an investigation, and that confirmed violations may result in disciplinary action up to and including termination. Governance authority, including decision rights, escalation paths, and role responsibilities for determining when and how actions are taken, is defined in the information security policy.
Standards of conduct and prohibited content
Include a brief section on the proper use of systems and explicitly prohibited behaviors, remembering to define the terms you want to use. This should be equal parts workplace conduct and security posture.
Why this matters
The AUP is instrumental in maintaining an organization's cyber posture. The weakest part of any security program is the people, and this policy aims to guide their actions to reduce risk. A well-written AUP reduces risk by clearly communicating expectations to users and managers.
Access control policy
The access control policy defines how access to systems, applications and data is granted, maintained, reviewed, and terminated. Its purpose is to ensure that only the correct people have the correct principle-based access at any given time.
When writing this template, don’t attempt to write a process for each system; write a process that is repeatable across systems.
Purpose, scope, and inheritance
As with the AUP, the access control policy should inherit scope, roles, and responsibilities from the information security policy; do not restate who does what in this policy.
Security model and principles
The template should require each client to state their access control model in clear terms, for example: least-privilege, need to know, or default deny. This will likely require a conversation with a client decision-maker to gain insight. This section is where you would state which principle the client operates on, but you must also define that principle. For example, if a client uses role-based access you would define those roles here.
Account lifecycle
The information security policy should define who is responsible for identity and authentication governance. This policy doesn’t need to repeat that; you can instead reference the information security policy for that information. This section of the policy focuses on the following:
- Provisioning: How access is requested, approved and created
- Modification: How access is changed upon request or during a role change
- Access review: How often access is reviewed and in what way
- Deprovisioning: How and within what timeframe is access terminated when no longer required
An additional section for elevated access should be included. The template should call for separation between standard and administrative accounts, support for just-in-time authentication where possible, and a strict access review process.
Logging, monitoring, and enforcement
Reference the roles and responsibilities section of the IS policy, which should define who is responsible for what in this context. State that access events and privileged access must be logged and monitored and that enforcement and investigation occur under the roles and decision rights defined in the IS policy.
Why this matters
A properly structured access control policy makes access decisions auditable, reviewable, and enforceable. By linking operational procedures to the authority and governance defined in the IS policy, this template supports consistent enforcement and reduces the effort needed to tailor this policy to a client's needs.
{{banner-small-1="/inline-cards"}}
Password and authentication policy
This policy defines how users prove identity before access is granted. Its purpose is to reduce the risk of unauthorized access caused by weak authentication methods.
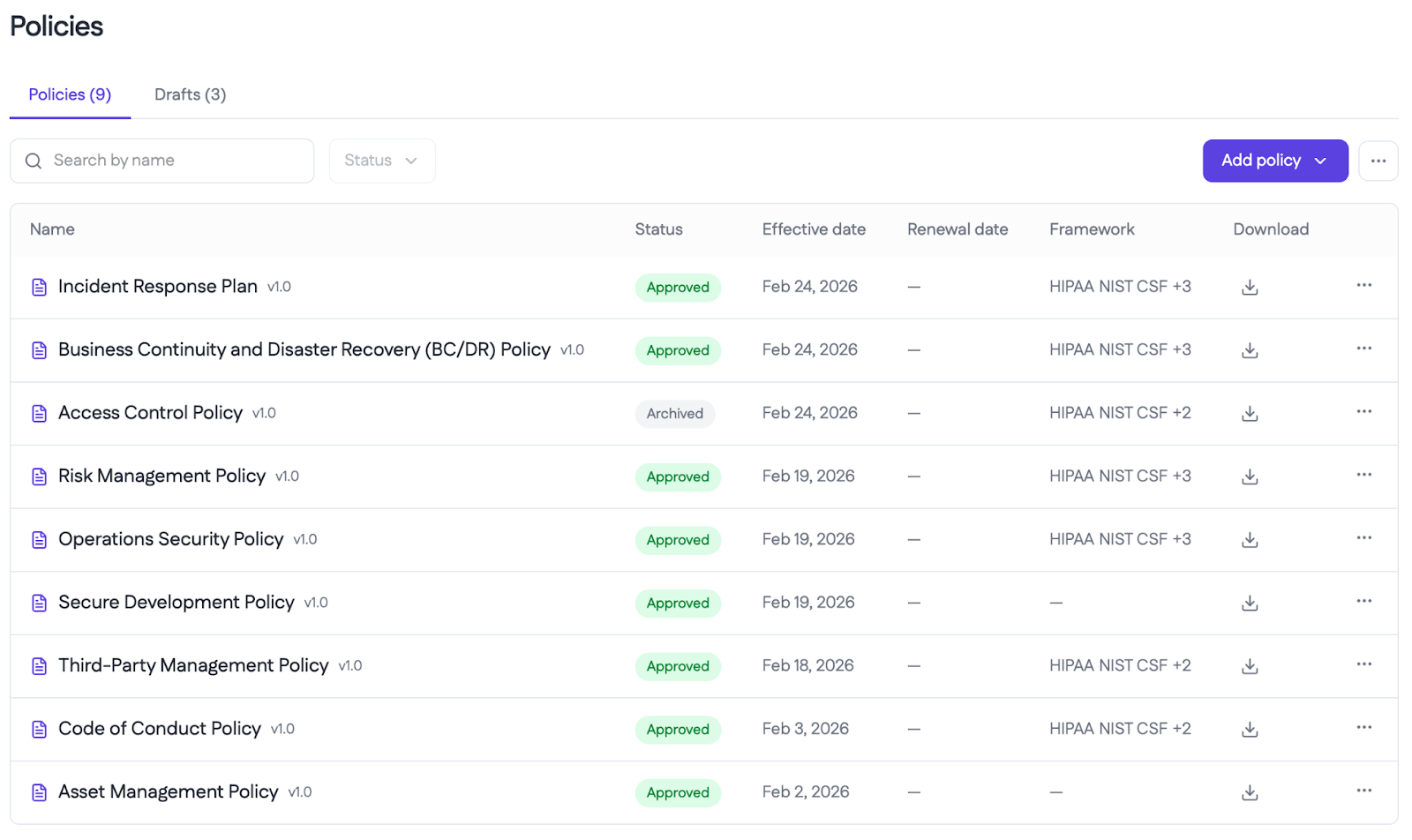
When writing a template for this policy, don’t mention specific technologies such as OAuth or Entra. The objective of this template is to define a decision framework and a minimum set of requirements for strong authentication that can be easily adapted to most situations without altering the template.
Purpose, scope, and inheritance
As with the preceding policies, do not restate the already defined scope, roles or responsibilities; simply reference the IS policy and focus on stating what this policy aims to define. As stated above, this policy’s purpose is to define the requirements for strong authentication. This section should state that and also state why that’s important to the organization and how it supports the objectives laid out in the IS policy.
Authentication requirements
This section is where you should define the minimum baseline required to be considered “strong authentication.” This section will vary greatly based on clients' and MSPs or MSSPs views on authentication. Keep these requirements realistic; do not place what you want your client to do here but rather what they have agreed to do.
Filling this section out will require a client touchpoint in some cases, where the client’s posture may be more nebulous than the security-minded among us would like. This section should include who and what MFA applies to and what is considered MFA. For example, is SMS still permitted?
Credential storage and handling
This section should define how credentials may be stored and protected. Note that this is another place where you want to put definitions in place. Don’t simply state “secure storage methods” or “approved methods”—be explicit about what those statements mean. If there is an approver for this, they should be defined in the IS policy.
Logging, monitoring, auditing, and enforcing
The template should require that specific events be logged, such as failed logins, password changes, MFA challenges, etc. The information security policy should already state who is responsible for these tasks; you want to use this section to define the procedure. Note that an incident response policy should define how monitoring should be escalated in the event of suspicious activity, not this document.
Periodic review
Require a review of the authentication requirements to ensure that they align with the organization's objectives and the current security landscape. These reviews are typically annual. Emphasize that without logging and auditability, one leg of the confidentiality, integrity, and availability triad is missing because controls cannot be validated or defended.
Why this matters
A properly created password and authentication policy makes controls explicit and aligns behavior with the AUP and incident response process. This template strengthens one of the highest risk domains while remaining adaptable to each client's circumstances.
Incident response policy
The incident response policy defines how the organization detects, responds to, escalates, and communicates during security incidents. The document also defines what constitutes a security incident.
When creating this template or adapting the template to a client, it’s very important to remain at the governance and expectation level and not delve into a step-by-step process. The step-wise process belongs in an IR playbook, while this policy should be referenced if your organization or client has playbooks.
Purpose, scope, and inheritance
Do not redefine who is in charge during an incident, who can declare an incident, who can engage external parties, or who can approve major actions. This document should explicitly reference those considerations and focus on how incidents are handled as a process.
Regulatory obligations
Most regulatory obligations—like SOC 2, ISO 27001, HIPPA, and those from cyber insurers—require organizations to have a formal IR policy. When templating this section, call this out as a compliance driver, but do not let compliance be the sole driver. The real objective is to ensure incidents are handled in a consistent, thoughtful manner.
Detection and classification
This section of the template should define how potential incidents are detected. Do not name tools here unless you are positive that they are ubiquitous in your managed environment. It’s best to use generic terms like “monitoring tools,” “user reports,” “third-party reports,” etc. This allows the template to require less rewriting while remaining relevant and useful.
This section is about requiring a classification step to exist and be documented. Who does that classification should be identified in the information security policy. Typically, this section will state that the service provider is responsible for this process.
Response and containment
At the policy level, you should have documented procedures for containment, eradication, and recovery. Those procedures should live in playbooks. The policy should simply state that response actions must follow approved playbooks, be documented, and consider business impact (not just technical remediation).
Escalation and decision control
This is one of the most critical sections, defining thresholds for action; who can take this action should be defined in the information security policy. The thresholds in play here would be legal impact, regulated data impact, operational outage, or any other metric tied to a business objective defined in the IS policy. This section exists to ensure that escalation happens in a predictable and auditable manner.
Playbooks
In a client’s policy, referencing playbooks is typically not recommended, as the playbooks should belong to the service provider and be referenced within their respective IR policy. However, there are many different types of management, and this may be a section required for some co-managed environments. This section should explicitly reference when playbooks are to be used and should cite the IS policy for who can make that determination.
Testing, evidence, and review
The template should require periodic testing, such as tabletop exercises. This section should define what is to be tested and at what frequency. It should also define the review of incidence and how the “lessons learned” process should work. Ownership of these processes should be defined in the information security policy.
Why this matters
A well-structured incident response policy turns chaos into a governed process. By anchoring authority in the IS policy and execution in playbooks, this template satisfies regulatory expectations, improves real-world outcomes, and provides the documentation needed to demonstrate due diligence and due care when incidents inevitably occur.
{{b-table="/inline-cards"}}
Final thoughts
Policies are not a checkbox exercise but a source of authority that lends clarity and protection to organizations. Good policies must reduce ambiguity, align responsibilities, and scale actress environments.
Together, these documents define a governed system. The information security policy defines the scope, intent, roles, responsibilities, and authority. Every other policy inherits this information. This design choice enables consistent, scalable results across clients and industries, preventing contradictions and gaps that lead to policy friction and program failure.
For service providers like MSPs and MSSPs, this model also forces clarity about provider vs. client responsibilities, decision rights, and escalation paths. If done properly and with the client's support, creating these policies can lend clarity, establish clear expectations, and build trust with the client to a degree that would otherwise not be possible at scale.