The Role and Functionality of a Modern vCISO Platform
In security operations, a vCISO translates information security challenges into business objectives, enabling strategic, business-oriented conversations between the vCISO and the client rather than purely technical ones. Communicating at a strategy level delivers additional value, builds trust, and helps leadership steer the organization towards reducing risk, increasing compliance, and measurable business outcomes.
Performing these functions for multiple clients at scale demands a full-featured vCISO platform: an integrated system to map risks and vulnerabilities, align with leading frameworks, gather systems data, and support decision-making.
This article will cover the scope and functionality of a modern vCISO platform, its must-have features, and also its role in scaling MSP and MSSP operations.
{{banner-large-1="/inline-cards"}}
Key vCISO platform concepts
The table below summarizes the key concepts covered in this article:
vCISO platforms for MSPs and MSSPs
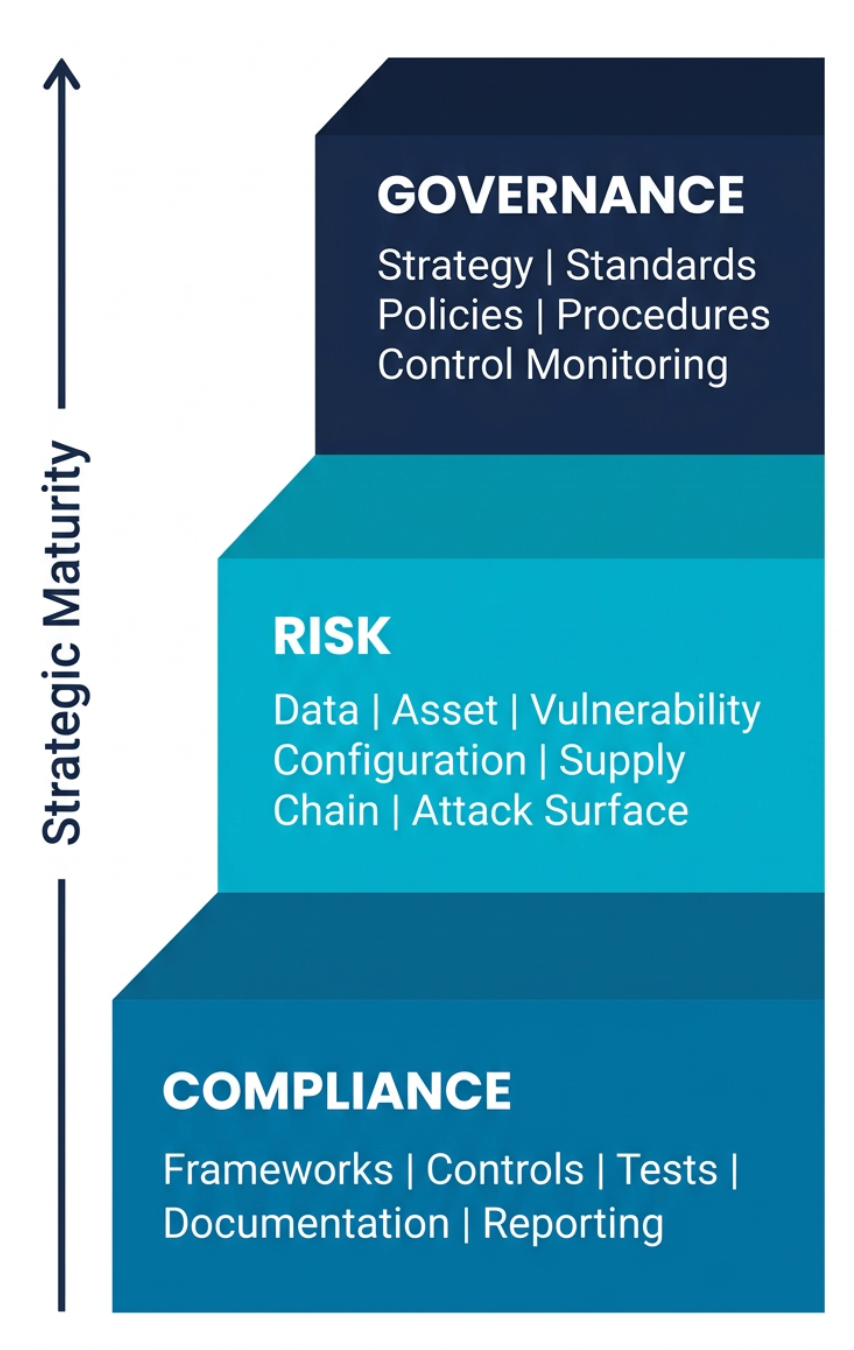
At its core, a vCISO platform helps vCISOs translate technical challenges into business objectives or business objectives into technical deliverables. vCISO platforms start with a single multi-tenant dashboard that centralizes risk, vulnerability, and compliance information, enabling security to be managed as a unified, business-aligned program rather than a myriad of technical challenges. Multi-tenant design allows MSPs and MSSPs to operate at scale while utilizing a single source of truth.
Business process and objective mapping can be aided by action plans, a crucial feature of a solid vCISO platform. These action plans use assessment results to convert findings into prioritized strategic and tactical tasks, with owners and dates assigned. Because the action plans are centralized and dated, they provide a basis for a running narrative for quarterly business reviews (QBRs) and updates, reducing preparation time and eliminating debates over status.
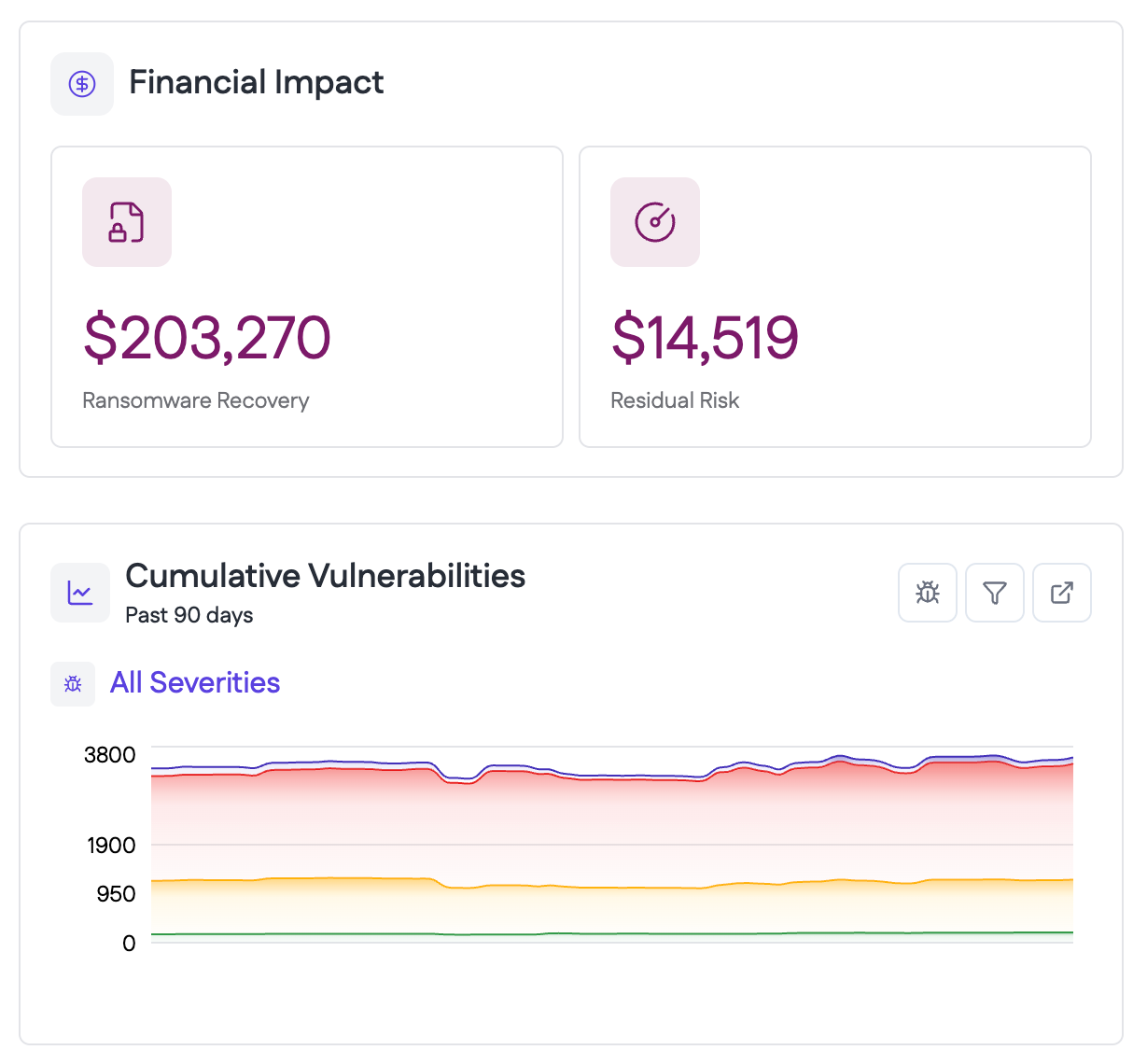
Risk monetization translates technical findings into financial and operational terms using the platform’s normalized data. This translation is essential to the vCISO role, as it ensures that both decision-makers and the vCISO are using a shared language.
A modern vCISO platform should include native compliance modules to map controls and gaps to standards selected by each client, such as PCI DSS, ISO27001, NIST CSF, or HIPAA. This lets the heavy lifting be done on the software side, so the vCISO can focus on strategic conversations rather than mapping frameworks to vulnerabilities.
By using scheduled scans and templated reports from the vCISO platform, the vCISO can leverage autonomously gathered data and remain at the strategic level. These reports can also drive business conversations with clients, the overall effect is an emphasis on business-level conversations that stay out of the weeds.
Action plans, along with automated remediation and professional services automation (PSA) integrations, can turn recommendations into tasks with traceable progress. This aids decision-making by moving the focus from what our options are to how we execute.
Business process and objective mapping
A modern vCISO platform helps vCISOs connect daily technical challenges to business objectives by creating data that prioritizes the business priorities rather than technical challenges.. This process starts with defining a lightweight process inventory (such as order-to-cash, receiving, or production) along with a small objective library (like regulatory compliance, customer trust, and revenue continuity). These labels can then be applied to assets, findings or action plans within the vCISO platform, which allows for direct, simple mapping that adds value and clarity to the vCISO process.
Assets can be associated with the business process they support within the platform. This ensures that when vulnerabilities are discovered, they inherit this context automatically. The association process further empowers decision-makers by providing business context about why a vulnerability matters (e.g., a vulnerability posing a risk to continuity of revenue or customer trust), allowing the conversation to remain strategic and not focused on the technical details.
Action plans can then be used to convert mapped findings into roadmaps, which are assigned and dated, allowing for greater transparency and providing a running narrative for client touchpoints, including QBRs.
A vCISO should remain at the strategic level, and one way to do so is by focusing on objectives rather than vulnerabilities themselves. By performing the mapping described above, vCISOs set themselves up for success by allowing the vCISO platform to create data on business objectives. Using an effective framework, vCISOs can filter items based on framework status or business impact; this selection is powered by the mapping functions. This data can then be used to prioritize remediation and to justify recommendations to clients. Without these tools, vCISOs can fall into the trap of recommending remediations based solely on technical severity, which can result in a loss of trust with a client, as they feel they are getting a one-size-fits-all approach.
Impact translation
Mapping process and objectives allows you to have a conversation where both the vCISO and the client are speaking the same language, but you can apply more context to the data and provide the client with insights about how exactly an event could affect the organization. The mapping process leaves you at e.g., “this affects revenue continuity,” but you can transform that into something like an hourly cost if more context is available from the client.
In practice, a revenue-bearing system no longer appears as a list of CVEs; once mapping is complete, that system is tied to a business process and can be discussed in terms of potential lost revenue, idle labor, and customer credits. Likewise, a misconfigured datastore isn’t just a technical misstep but is tied to customer trust and examined through the lens of estimated notification expenses, investigative efforts, and reputational or compliance exposure.
A vCISO platform will not be able to make declarations like what reputation exposure could be because each business case is unique, but it does allow for systems to be tied to processes and objectives, which drive relevant conversations between the vCISO and the client. Those conversations between vCISO and client executives are what empower these more in-depth metrics and impact translation.
The translation function is vital, as executives approve priorities based on business outcomes, not CVSS scores. When findings are expressed in dollars and operational consequences, the dynamic shifts from selling fixes to partnering on business decisions. Without that shift, a vCISO engagement inside an MSP or MSSP can be perceived as a conflict of interest at worst and a sales pitch at best. Using client-specific context ensures that the numbers reflect their reality, which leads to decisions they trust and value they can see. It also creates legitimate, billable work tied to measurable results.
Done well, impact translation reframes the relationship so choices are based on business impact rather than technical severity alone. It has become a cornerstone of a successful vCISO program. With the client’s cooperation on assumptions and data, the program strengthens credibility and accelerates approvals. Without it, the initiative risks being misunderstood and damaging the relationship by appearing primarily sales-oriented.
{{banner-small-1="/inline-cards"}}
Framework alignment
Framework alignment turns security items and controls into a program that clients recognize and auditors can verify. vCISO platforms assist vCISOs by connecting collected evidence and assessment results to the framework chosen by the client, selected per tenant, such as ISO 27001, NIST CSF, HIPAA, or PCI DSS. Findings are associated with the relevant control requirements, identifying gaps and offering remediation recommendations. Items are organized so they can be tracked in action plans and reported consistently during QBRs and audits.
Here’s an example process for ISO 27001 alignment:
- Select ISO 27001 as the governing framework for that tenant.
- Associate the existing evidence.
- vCISO framework highlights unmet requirements and organizes them into tasks.
- During client reviews, the vCISO shows current status by control family, the evidence on file, roadmaps, etc.
The result is a defensible, client-specific program that allows for easy scalability and provides value to clients. This combined effort strengthens credibility, shortens approval cycles, and turns a framework into measurable value that executives can use to visualize progress.
Evidence reporting and automation
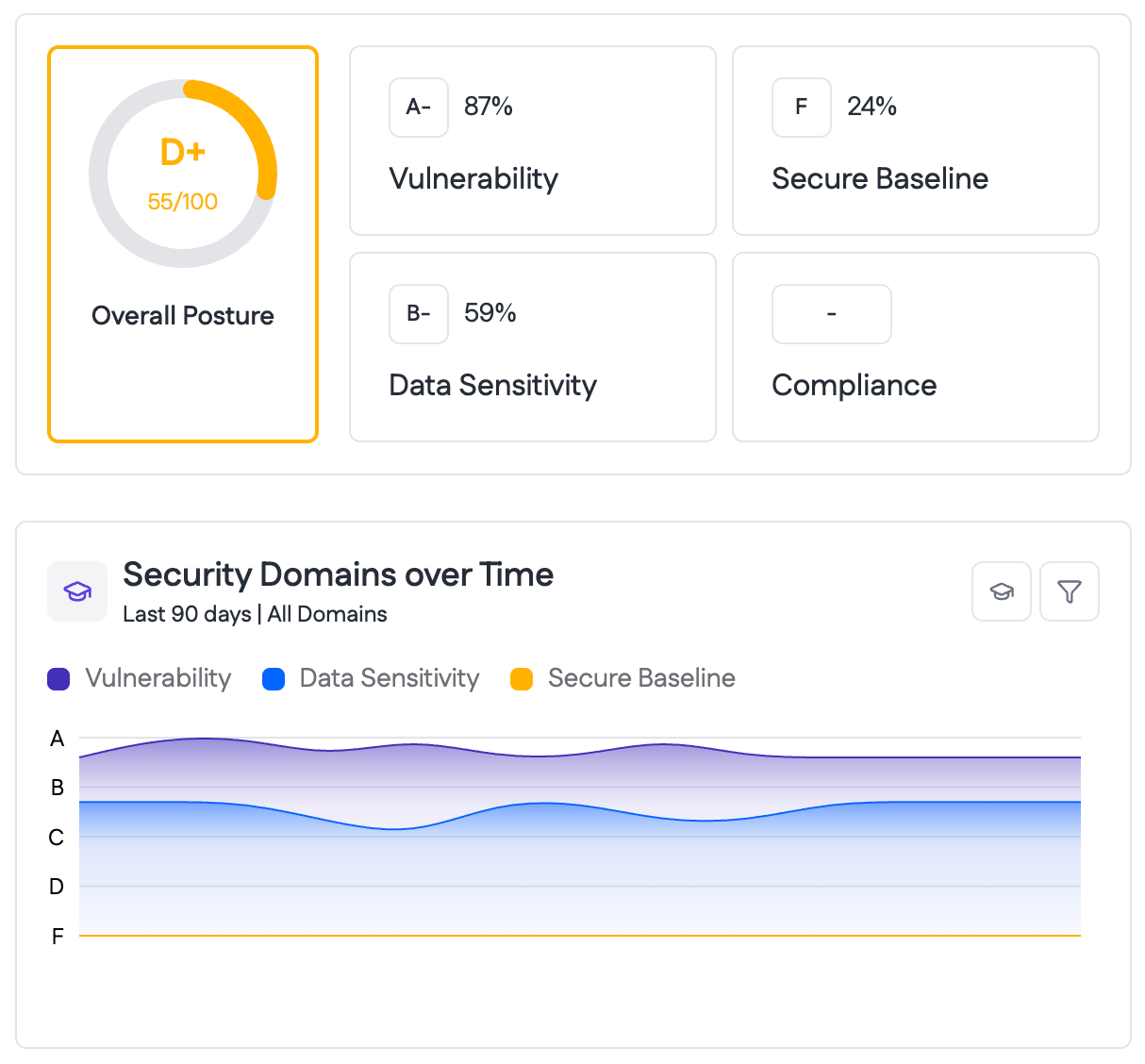
This function turns a vCISO program from a labor-intensive trudge into a clean, repeatable, and scalable process. Replacing manual scanning for a modern vCISO program is a must to remain competitive in the MSP and MSSP space. Typically, collectors will be scheduled to perform scans on at least a weekly basis (ideally, continuously) to ensure that the data the vCISO is using to make recommendations and decisions is accurate and up to date.
Evidence gathering feeds all of the processes we have covered so far; however, it's the one area that the vCISO shouldn’t be involved in. The deployment and configuration of collectors should be left to MSP and MSSP assets, which are focused on technical tasks such as systems administrators or security analysts. This separation allows the vCISO to live on the strategic level, enhancing the value they bring to clients.
Once automated scanning is in place, a vCISO platform can be used to assemble reports from the collected data. These reports are typically templated and allow for a clean, repeatable item for use in QBRs and other client reviews. Because the narrative remains focused on current data reviews, it is necessary to stay focused on current items and decisions and avoid the common pitfall of scope creep. For MSPs and MSSPs, this reduces the prep time per client, increases consistency, and enables the organization to support more clients without sacrificing quality.
Decision support integration
After mapping objectives, translating impact, and aligning to frameworks, decisions still need to be made, recorded, and executed. vCISO platforms help vCISOs do this at scale by turning analysis into owned work, moving that work into operations, and retaining transparency with the client on progress.
First, vCISO action plans convert assessment results into prioritized items with owners and dates. Decision meetings get a concrete menu of choices that specifies what to do, who will do it, and when it will be done. Approvals focus on sequencing and trade-offs instead of open-ended debate. The same plan serves as a single, auditable record of the decisions made.
Then, risk monetization views add business context next to the plan. When alternatives are reviewed, leaders can see relative impact and effort in one place. This shortens the decision-making time and reduces the need for ad hoc spreadsheets during QBRs and MBRs.
Next, PSA integrations push approved actions into tickets with SLAs and workflow. This not only enables transparency with the client but also ensures a record of the work is maintained. Operations teams gain clear ownership, while the vCISO and client can monitor progress and stay at a strategic level.
Following that, framework alignment and reporting keep decisions tied to obligations that executives and auditors recognize. Status by control family, evidence on file, and planned remediations are presented the same way each cycle. This increases transparency and reduces surprises.
Finally, vulnerability and remediation workflows, such as additional scans, provide validation that work actually happened. As items close, evidence attaches to the record, and dashboards reflect real progress rather than intentions.
For MSPs and MSSPs, this combination accelerates approvals, strengthens accountability, and standardizes communication across tenants. For clients, the experience shifts from a list of issues to a documented and repeatable program that ties investment to measurable outcomes.
{{b-table="/inline-cards"}}
Last thoughts
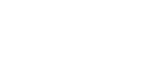
A modern vCISO program succeeds when security strategy is expressed in business terms and executed with repeatable precision. Throughout this article, we discussed how a platform-centered approach enables MSPs and MSSPs to manage multiple clients from a single source of truth, turning tool outputs into objectives, roadmaps, and auditable results. Process and objective mapping keep priorities anchored to business objectives such as revenue continuity, customer trust, and regulatory obligations. Impact translation adds client context, so leaders can compare options by cost, downtime, and exposure rather than scanner scores. Framework alignment organizes evidence against recognized standards and creates a common language for executives and auditors. Evidence automation and templated reporting maintain a reliable cadence for QBRs and audits, while decision-support features convert approvals into owned work with clear accountability.
When used as a tool to help clients achieve their business goals, the vCISO role moves beyond ticket closure to delivering business outcomes and building strategic partnerships. Clients gain clarity and trust, approvals accelerate, and your team scales delivery without sacrificing quality.